From
his home, hacker Amador Aparicio could open the floodgates that empty
the retirement pond. or change the pool temperature of a luxury hotel.
Spain is the fifth country in the world with more systems that control
all kinds of installations and industrial processes connected to the
Internet, most without any protection. The most sensitive, critical
infrastructures, are being harshly ciberatacados, with an increase of
357% last year. And, according to experts, this figure is short.
Amador
Aparicio usually lectures on cybersecurity. I was preparing one, about
industrial control systems, when I ended up with the stuff I could do at
a distance, how to start the crematory furnaces of a morgue, decide
from what ambient temperature the heating of a higher school will start,
or to disable the alarms that warn of excessive pressure in the boiler
of a block of houses.
These
cyber are also quite easy, says Amador: "If you want to locate unsafe
industrial control systems, the first thing is to know the manufacturer
and, with this data, go to a finder of devices connected to the Internet
as Shodan". In seconds, Shodan displays a list of vulnerable systems,
including its GPS location.
The
following is to get the ' software ' management that uses the device
you want to attack, to install it on the computer itself, so that the
computer of the hacker and the attacked device "speak the same
language". According to Amador, these programs can be obtained many
times on the same page of the manufacturer, which is poorly protected
and allows to unload what one wants.
"The
last step is to connect to the device," explains the investigator,
something also relatively easy because, he says, "many devices that
control industrial processes or critical systems do not present any type
of security Configuration". Once inside, you can modify the operation
of the device, either changing the parameters that start the system (for
example to make it activate from the temperature you want), or modify
the information you have in memory, to do unexpected things.
Without knowledge or without care
Aparicio
blamed this lack of security that "the operator who put them on the
internet did not have the knowledge or has not thought that anyone can
access." Other devices are protected, but "with the default data that
shows the documentation", data that anyone who has read the manual can
know. Another problem, says the investigator, is that "each manufacturer
uses its own protocols, insecure on some occasions, and there is no
standardization when integrating them."
José
Valiente, director of the Center for Industrial Cybersecurity (ITC),
adds: "There are a growing number of automated and externally connected
processes and installations, in many cases over the Internet;"
"Everything has increased in industrial automation, complexity, use and
exposure of systems, but cybersecurity is not the same."
The fifth country with more connected systems
Spain
is the fifth country in the world with more industrial control systems
connected to the Internet, 3,059 when it comes to writing this article.
But how many securely? In this context, the essential service operators
and critical infrastructures are particularly concerned. Malicious
hackers could poison our water, sabotage nuclear power plants or leave
us without light, just to put examples that have already happened in
other countries.
Last
year, 479 cybersecurity incidents were detected in critical
infrastructures located in Spain, an increase of 357% compared to 2015
according to the National Center for the Protection of critical
infrastructures (CNPIC), that relativizes this alarming fact: "in 2016
has increased the number of critical operators, also the capabilities of
the cert of security and industry and the level of confidence in their
relationships with critical operators" , which has resulted in an
increase in notifications. "
Still,
the increase is remarkable and that, says José Valiente, "have not
detected 10% of the incidents that are occurring." The probes that
collect these data analyse only 10% of the traffic of a hundred critical
operators, explains the director of ITC. "If Inspeccionasen the other
90% of traffic we would be talking about more than 4,000 incidents in
only these 100 operators". And if we include all essential service
operators, more than 5,000 in Spain, "then we would talk about at least
100,000 technological incidents," says Valiente.
The
critical services most attacked in Spain are, according to a study by
ITC that will soon see the light, "the health sector, which has
registered more than 40,000 incidents;" "followed by energy, due to the
use of very recent technology in the smart grid."
The
' annual National Security Report 2016 ' highlights that the incidents
of cybersecurity in Renfe "have experienced an exponential increase",
but the director of ITC clarifies it: "The transport sector in Spain is
one of the best security level has, especially the aeronautical." The
ITC study has evaluated different sectors and, according to Valiente,
RENFE obtains the best qualification.
The power grid is the big concern
But
the great concern of Western governments is the power grid. And his
nightmare is to suffer a attack like that that left seven hours without
light to Ukraine in a cold December of 2015. Could this happen here?
"Once such incidents occur, it is difficult for them to repeat
themselves, but the measures to ensure that they are not replicated are
not adopted within a few months, so I do believe it would be possible,"
says ITC director.
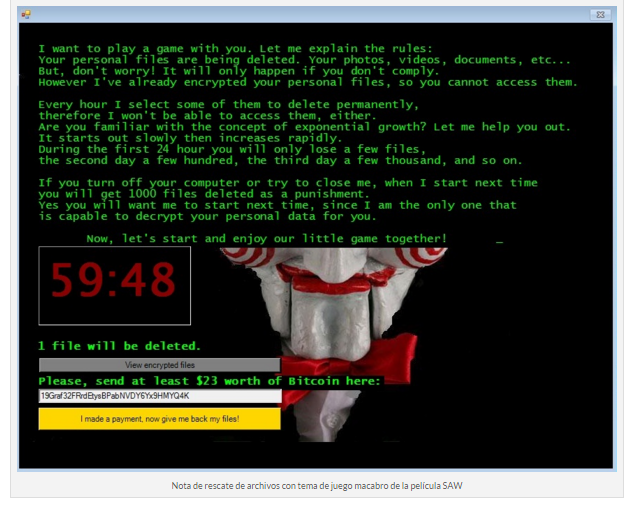
A
virus called BlackEnergy played an important role in the attack on
Ukraine and, according to sources of Cnpic, certainly viruses and
malicious programs are responsible for most attacks against Spanish
critical infrastructures. Their goal is usually to steal information,
blackmail (case of ' ransomware ') or manipulate legitimate programs.
The
most frequent incidents are those that leave no trace (for example,
theft of information) that we do not discover until past months, years,
or never
The
second large group of incidents against critical systems detected by
the cnpic are the bombardments or "denial of service Attacks", whose
intention is that the service stops working. Like all over the world, in
2016 have rebounded the attacks of ' ransomware ' and ' fraud to the
CEO ' also in the Spanish critical operators. In addition, they explain
from the cnpic, "from the hand of Europol several collaborations were
carried out in the fight against the botnets". Fortunately, they
congratulate themselves, "all incidents were detected, managed and
resolved in time."
Other
observers are not so optimistic. From ITC They remember that the
statistics we know are of visible things, like attacks that cause a fall
of the service or a malfunction, but the most frequent incidents are
those that leave no trace, the theft of information, the alteration of a
' software ', a service, etc., that we do not discover until months,
years, or never have passed, says Valiente.
The case of the United States
In
the United States, the defense of its electrical network and experts
working on it are taking a particularly serious view of the vision of
Valiant, as Michael Assante: "We are entering an ERA in which more
actors are able to have the right skills, energy engineering in addition
to cyber engineering and access skills." This leads to very targeted
attacks against critical systems that may take weeks or months to be
detected.
The
attribution of these attacks is very difficult, they assure our sources
of the cnpic, but if it is possible to see that "the complexity and
sophistication of the attacks increases year after year", this implies
that after them there is not an isolated individual but, according to
the Cnpic, "highly structured organizations, with specialization in the
different tasks necessary to build a attack and invest a great amount of
resources". Attacks of these dimensions can only be borne by
millionaires, large corporations or governments.
In
this league, the defense also requires the strength of a government and
it is fair to say that the Spanish is quickly getting the batteries. As
a token, the Critical Infrastructure Protection Act, the National Plan
for the protection of critical infrastructures, the creation of agencies
such as the early Warning service for industrial systems or the new
cybersecurity coordination centres in RENFE and port authorities, or the
collaboration of public and private actors in environments such as the
cybersecurity coordinating table and the production of documentation
such as the "Ciberincidentes Report guide for critical Operators".