The
operation of the ransomware is very simple: it's just a malicious
program that encrypts the computer's boot files or, at least, the part
where you have all the data you want to steal and usually gets '
inoculated ' through downloading a file, although it's not the only way.
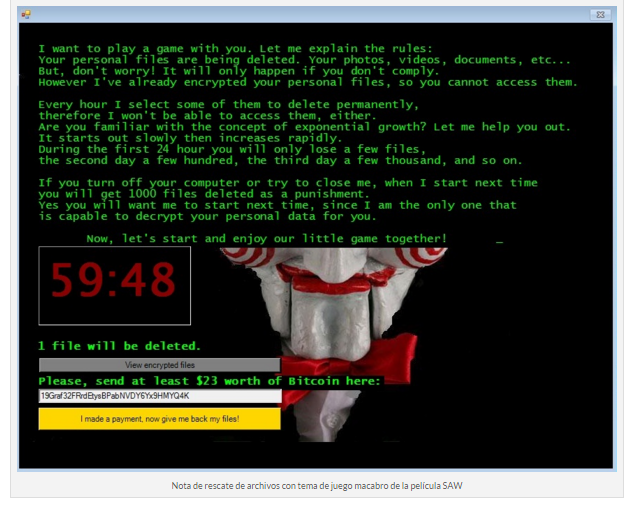
This
software, downloaded or remotely installed, ends up blocking the
system. A notice appears on your computer screen, where you are informed
that you have been infected and how to proceed to pay a ransom as the
only solution. The computer, from that moment on, is completely
disabled.
Usually,
the hacker usually ask for the ransom in bitcoins, being much more
difficult to trace for the security services. Once the payment has been
satisfied, the theory says that the thief releases the retained data or
at least provides the user with a code with which to get access to his
own information again.
But
it's not always like that. It is possible that this is just a strategy
of the ciberdelicuente to get money and that, once it succeeds, it does
not have the slightest intention of returning the control of the
computer to the user. Therefore, it is advisable to never give in to
these pressures.
In
fact, the authorities recommend that whatever happens, never pay the
hackers, because not only gives them confidence to continue committing
more crimes similar, but can make you lose a large amount of money
without knowing that this hole can be fixed in a simpler.
The
table of salvation before this attack is nothing more than having a
backup: having, it is as easy as formatting the computer and
reinstalling it to recover the activity in total normality. With these
simple steps, you recover without any cost to the activity on the PC.
That
yes, there must always be a complaint in the middle, because it is
necessary to remember that the data stolen, in the power of hackers,
allow them to trade with them or use them as they deem appropriate,
being a vulnerability of privacy that must be communicated to the
police.
The
attack with ' Ransonware ' has become one of the most dangerous and
habitual of recent times, which takes advantage of the scarce
predisposition of the user to make a backup to create a problem. A
non-copy database is a gift for malicious people on the net.
0 comentarios: